All-in-onesecurityhygiene.
Comprehensive cyber security. For your entire business. Out of the box and hassle-free.
Perfect for your business - Cloud, Windows, Mac and Linux.
Monitoring
Unified security monitoring for your entire organisation. Query your infrastructure like a database. Instant answers to your toughest questions.
Risk
Measure your risk in real-time. Stop guessing where your cyber-security risks lie. Get deep insights into every facet of your organisation.
Compliance
Industry compliance and policy frameworks managed like a task list, maintain compliance all year round. Let Zercurity do the heavy lifting.
Benchmarking
Benchmark your companies security against the industry, learn to make improvements and track progress over time.
Over 1000 companies already use Zercurity.
We take the hassle out of cyber-security compliance and risk.
.01 Fintech
The biggest challenge our customers face when implementing cyber-security best practice is the time spent stitching different vendor solutions together and not securing systems.
Key Requirements
- Ensure company compliance against CIS
- Monitor new assets that join the infrastructure pool
- Manage employee device risk
- Proactive cyber defence
How Zercurity helps
- Deploy to every end-point quickly with no disruptions
- Aggregate the data into actionable prioritised actions
- Lifetime history of all data for triage
- Vulnerability scoring and remediation
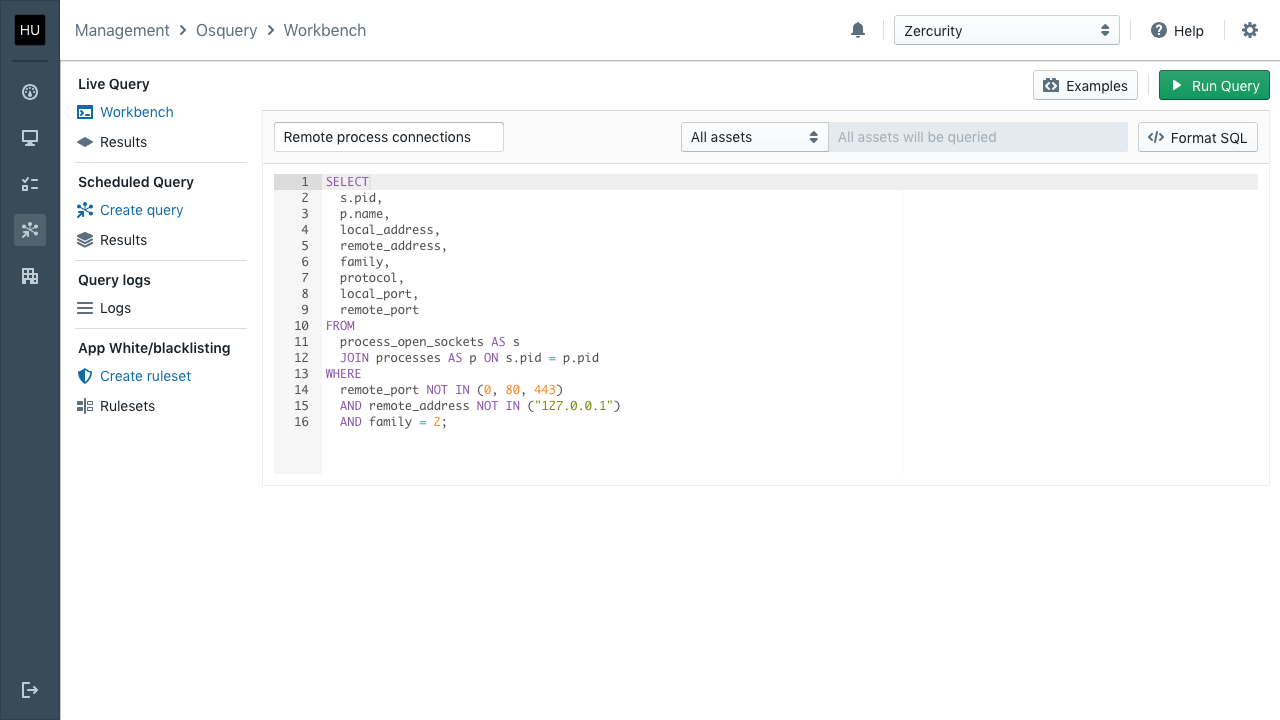
Ask any question
Setup scheduled queries to meet weekly, monthly or daily compliance and get alerts straight to your phone.
Setup scheduled queries to meet daily, weekly or monthly compliance tasks and get alerts straight to your phone.

Quick deployment
Zercurity deploys Osquery automatically with every enrollment, which means you get the number one open source security tool, pre-configured and ready to go.
.02 Legal
Dealing with case-critical data across multiple employees is difficult to monitor, let alone manage, the last thing you want to do is prohibit or slow down access to crucial information.
Key Requirements
- Monitor data flow between systems, emails and people
- Secure private case files
- Instil good security practice with employees
- Monitor for vulnerabilities
How Zercurity helps
- Track applications and devices plugged into company equipment
- Monitor server infrastructure for abnormal activity
- Protect sensitive client data to outside exposure
- Real-time alerts and actionable reports
Dashboard
See the metrics that are important to you in real-time. Drive down into critical areas and remediate faster.
Reporting
Automated alerts, reports and scoring to create measurable attributes across your cyber-security posture. Zercurity gives you visibility so you can build protection.
.03 Insurance
Stabilising your client's risk exposure is a win, win. The client practices better cyber hygiene and in turn can get a better more dedicated product and you as the insurer get higher quality metrics upon which to make an assessment.
Create better more targeted products with a tool your customers will love. Practice better cyber-security hygiene and lower cyber exposure risk. Protected with Zercurity and safe with insurance.
Key Requirements
- Lower the chances of a breach for your clients
- Grow cyber insurance as a product
- Offer clients guidelines they can measure
- Smarter premiums based on activity
How Zercurity helps
- Identify gaps as they appear
- Build cyber best practice into your business
- Composite risk, vulnerability scoring and industry benchmarking
- Compliance adherence frameworks and reporting
Immediate Health Assessment
Start enrolling assets for Windows, MacOSX and Linux.
Or connect your cloud or SaaS provider. Get results in minutes.